Purpose-Built for Microsoft 365 Security
Get more from the Microsoft security tools you already own. Siemserva surfaces what matters across every domain. One scan, one view, one tool. Combine our 650+ checks with Microsoft Zero Trust Assessment and Maester, both plug in as first-class integrations. Your own PowerShell scripts drop in with zero code changes: emit a Senserva JSON file and they land in the same graph, no SDK required. Want deeper access? The Senserva SDK exposes the full graph in C#, Python, and PowerShell. Every source, native or external, maps to the same compliance controls, dashboard, and AI reports.
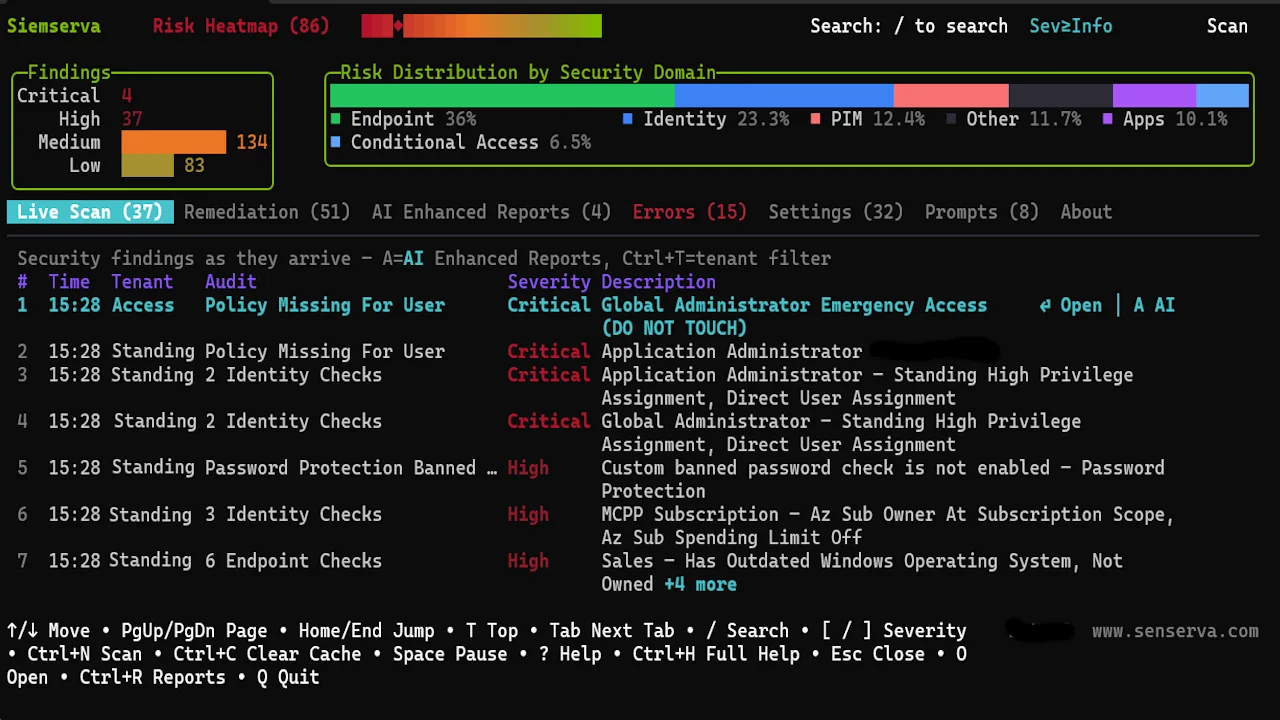
650+ checks, every Microsoft 365 surface.
A sample of what Siemserva looks at. The real list is long. Run the demo to see it.
- MFA and phishing-resistant auth
- Conditional Access gaps and bypass paths
- Privileged roles and PIM
- Legacy auth still permitted
- Guest and external access
- Intune compliance and baselines
- App registrations and Graph scopes
- Email: DMARC, DKIM, SPF, Safe Links
- SharePoint, Teams, OneDrive sharing
- Unified Audit Log and alerts
- Copilot and AI agent governance
- Purview sensitivity labels and retention
- Patch posture: missing patches and CVE exposure
- MCSB and CISA SCuBA mapping
That is a dozen out of 650+. Want the rest? The demo tenant walks through every finding with real data.