When you get the Key. Run the wizard. Pick your data. Go.
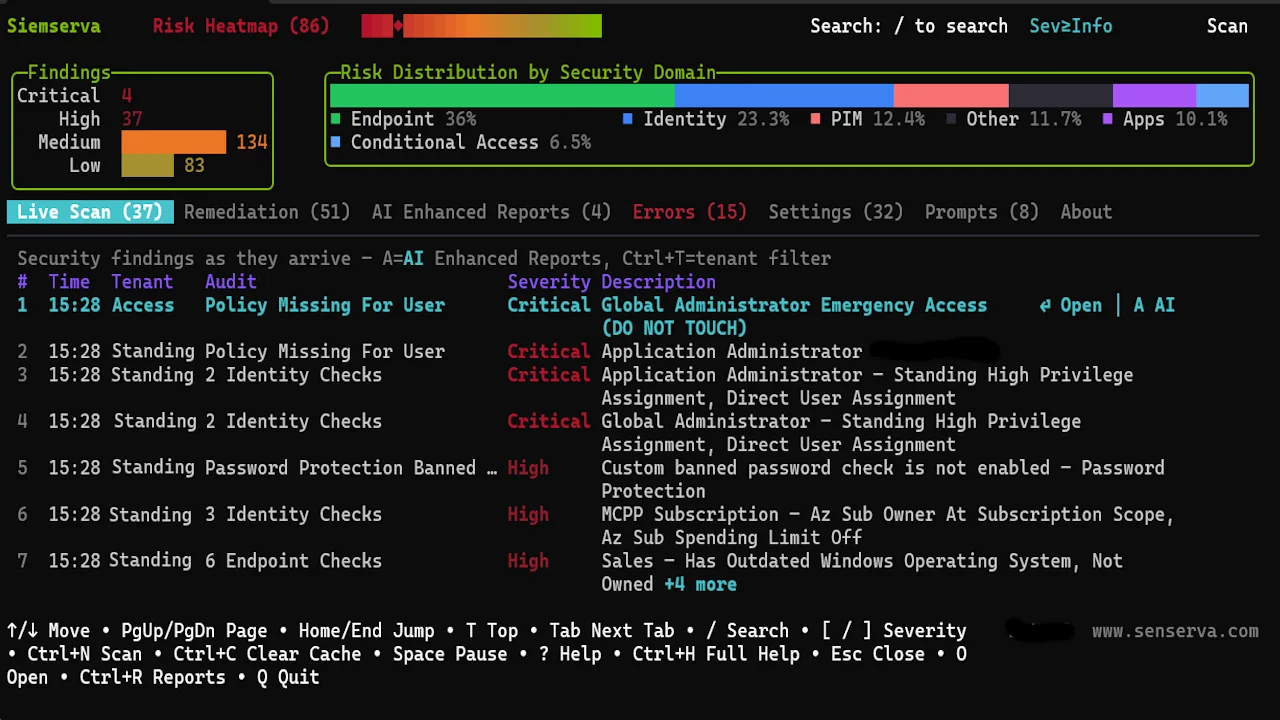
Run siemserva-win-x64.exe or ./siemserva-osx-arm64 with no parameters. Three short steps and you are in.
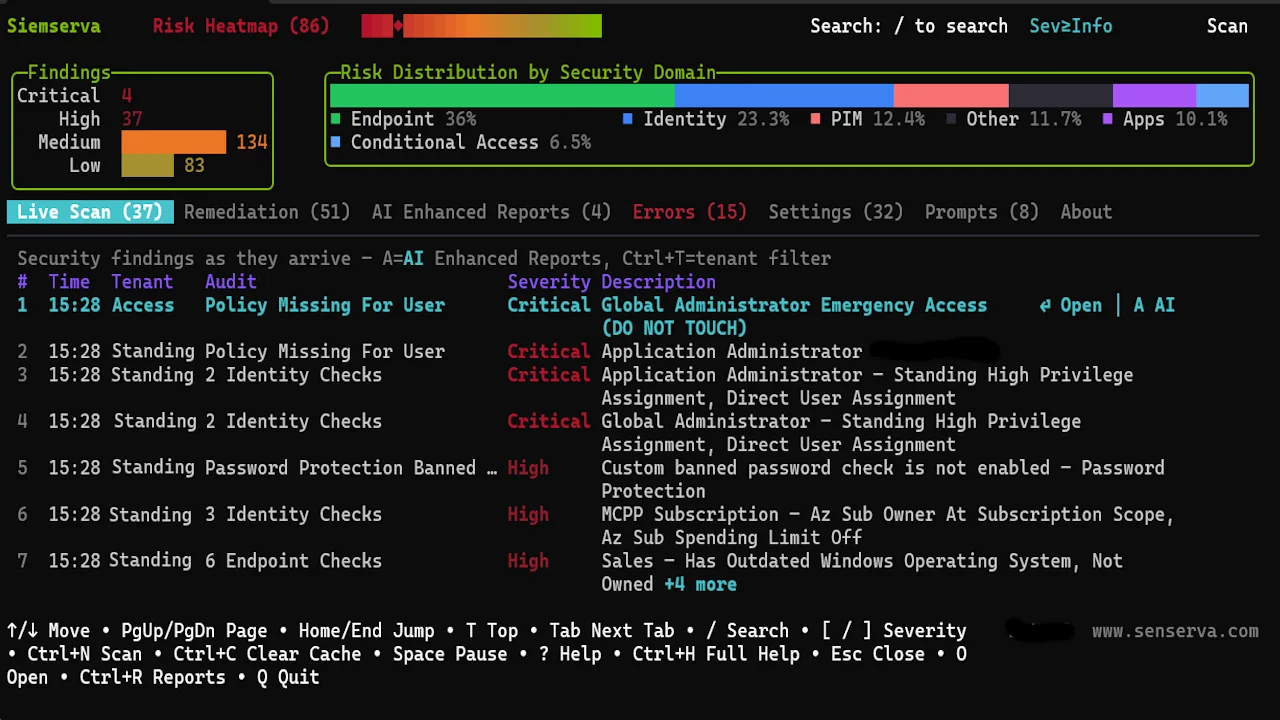
Run siemserva-win-x64.exe or ./siemserva-osx-arm64 with no parameters. Three short steps and you are in.
Note · safest way to try it
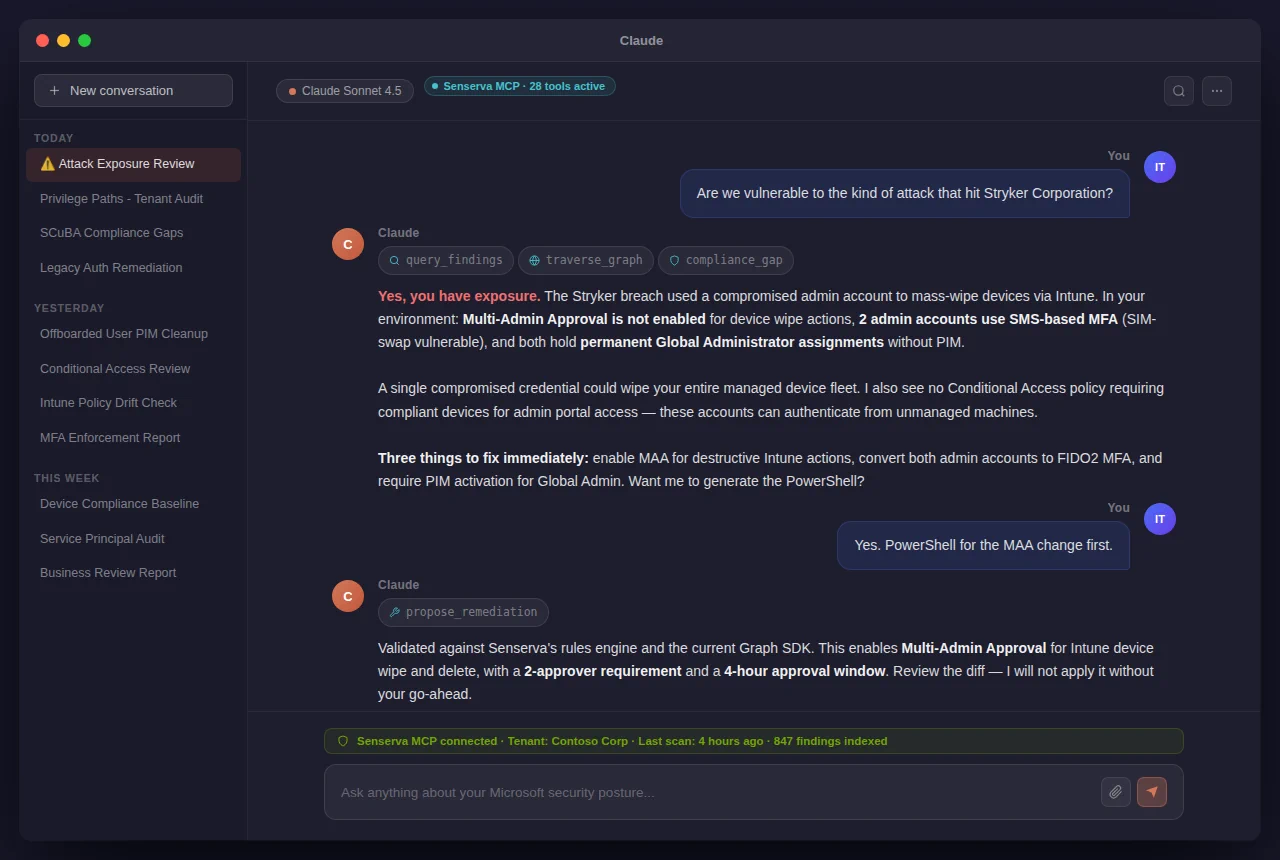
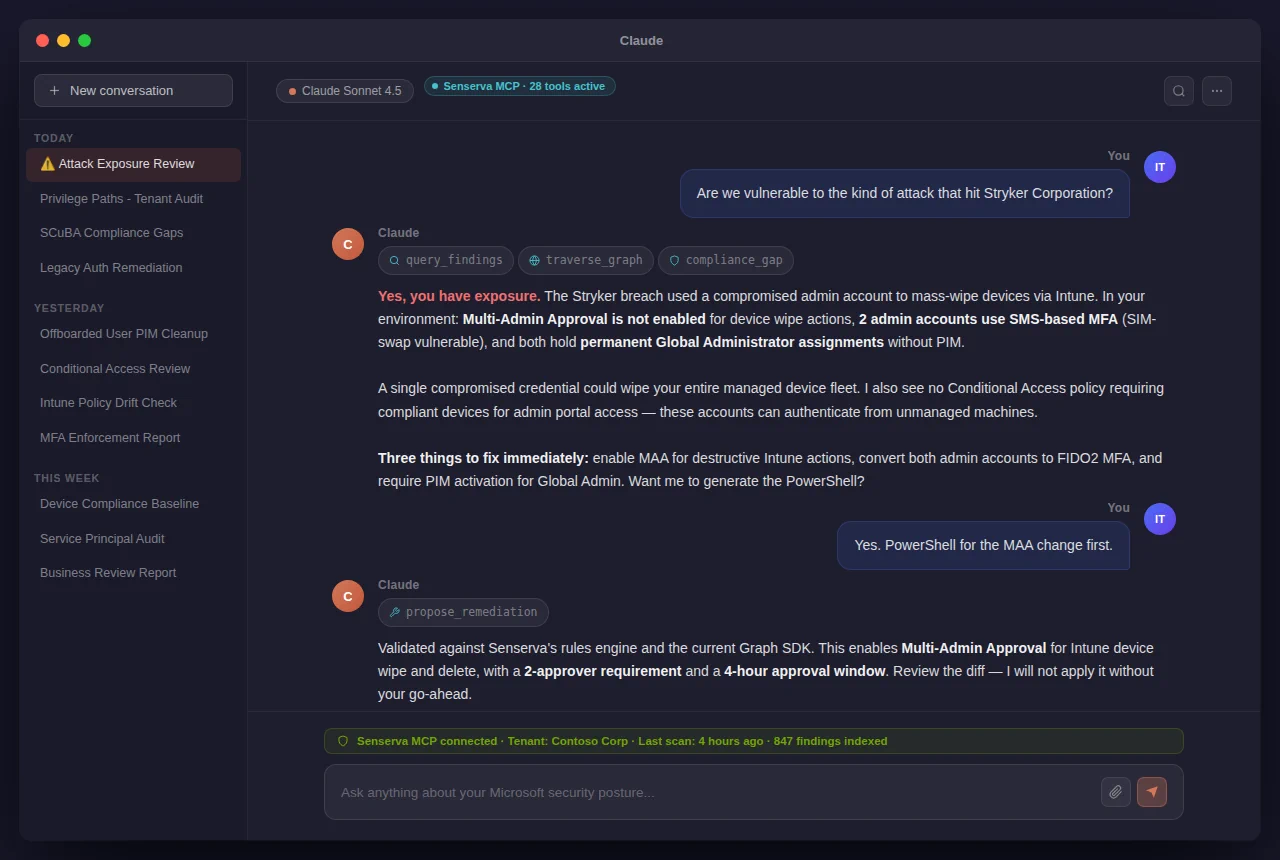
If you want to evaluate Siemserva and Claude without touching your real machine, run them inside Windows Sandbox. Spin up a fresh sandbox, install Claude Desktop, then install Siemserva. Delete the sandbox instance when done.
We use Google Analytics cookies to understand site traffic. No findings, scan data, or tenant data are sent. Privacy policy.